Manual Discovery and Removal of Malware
Posted by William Diaz on October 6, 2010
If you have not had a chance, set aside some time to watch Advanced Malware Cleaning, an excellent webcast by Mark Russinovich. I used some of the techniques from that presentation to identify and remove malware on systems I have come across.
In the case here, the user would open Internet Explorer but was not able to connect to the Internet. This would happen a couple times a day. The problem was tracked down to the Proxy field not populating with the office ISA address and the field remained grayed out so it could not be toggled on directly. The issue could be worked around temporarily by editing the registry to enable the proxy but at some point it was getting removed again. I was already suspicious that this was related to malware because each day the user logged on, the virus protectionsuite would catch the same Dlls’ attempting to downloaded to the system and being deleted.
I would be using Process Explorer and Autoruns as my tools. Here were the first things I noticed:

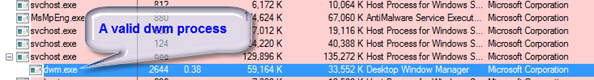
You probably already know that malware often runs multiple processes so I visually scanned for other suspicious programs. These were not too difficult to spot:

Shell.exe sounds valid but it’s also malware. The Windows XP user shell is actually explorer.exe, not shell.exe; shell and shell32 are actually dlls.. Dwm.exe is a real windows process otherwise known as Desktop Window Manager, which is responsible for managing the aero display, but only on Vista and Windows 7 systems; it has no place on an XP system. Also, dwm.exe is a child process of svchost.exe, not explore.exe. And finally none of the processes could be verified as coming from Microsoft (using the Verify button in the properties of the process).
You can also look inside suspicious processes for hints on its purpose, intent, or smart-ass remarks from the author. I double-clicked shell.exe and went to the Strings tab*:

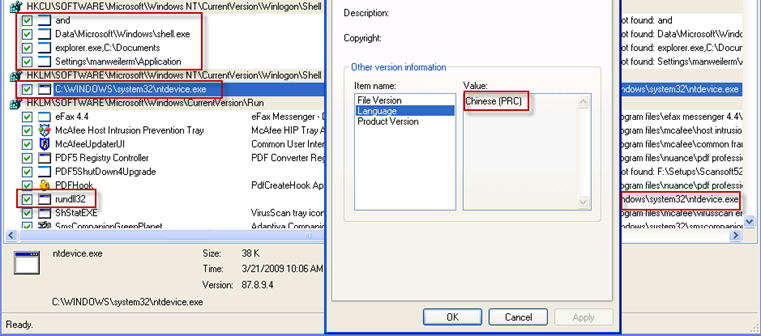
Here I can see a reference to one of the other malware processes in shell.exe, dwm.exe and, more importantly, URL links to some suspicious sites, including a couple Chinese URLs, which probably indicates the country of origin. In another suspicious process above, ntdevice.exe, I can see references to suspicious dlls. These are the same dlls’ that our anti-virus suite was deleting when they were downloaded.
And, looking at dwm.exe again, I see it has an open port. It was likely communicating with any number of URLs like those in shell.exe, likely attempting to download the same dlls that were being deleting:

After isolating the offending processes, the next step would be to shut them down and delete them from the system. Before doing this, though, it’s important to note that malware processes have watchdogs, are watchdogs for the other malicious processes and actively look for their companions and will restart them if they are killed. To confirm this, I killed shell.exe and watched it start up again. To work around this, Process Explorer allows you to put the processes to sleep by suspending them. Once they’re asleep, kill each one and go to the image path and delete it. If any malicious processes were missed, you will likely see the ones you killed come back to life and you will need to find the other malicious processes/watchdogs you missed and repeat.
Next I started Autoruns and went through each entry looking for suspicious startup items. Since the malicious exes were already deleted, I expected to find a lot of “File not found.” I would delete these anyways. I was mostly interested in entries that I may have missed; mainly hidden tasks but I could not find any. But looking at the properties of one of startup entries, ntdevice.exe, I can see its its origin is, in fact, Chinese:
At this point, I ran a manual scan of the workstation with the virus scanner for good measure. Initially, this turned up nothing using the express search locations. But it’s important to note that malware can get backed up into Windows restore points and since this had been happening for a couple days I was likely going to find something there. So I pointed the scanner at the Windows restore points, a few items were found, and a reboot was issued to have the objects deleted. I followed up by using Process Explorer again after reboot to make sure nothing suspicious returned.
*It’s worth noting that more advanced malware can be packed or encrypted on disk so you should view the strings in memory by selecting the Memory option in the Strings tab (a packed image will be denoted in purple in Process Explorer by default.

Leave a comment