Here is a quick guide to some methods for defeating malware after you have been infected. I have used all of these myself (with the exception of the Desktops utility mentioned below) to successfully isolate and remove malware after it has found its way onto the computer. Read the rest of this entry »
Posts Tagged ‘Malware’
Some Strategies for Defeating Malware After the Fact
Posted by William Diaz on August 2, 2011
Posted in Troubleshooting | Tagged: Malware | Leave a Comment »
Manual Discovery and Removal of Malware – Internet Security 2011-2012
Posted by William Diaz on May 19, 2011
Sometimes you have no choice but to approach malware infestations manually, even when running an AV program. Generally speaking, AV relies on malware definitions to detect threats and, if your definitions are not up-to-date, you can get hit by a Trojan, virus, or worm. Even with up-to-date definitions, you are still open to attack by the latest threats for which signatures do not yet exist. When this happens, you need to manually discover the threat and remove it. Such was the case in an earlier blog.
In the example here, one of our users was infected during a “drive by” while browsing the Internet. Our enterprise anti-virus failed to detect the threat and manual AV scans of the system failed to remove it since there was no definition for it yet. This is one of several variants of fake anti-virus (Scareware) from the Braviax suite, XP Internet Security 2011, which presents various security window pop-ups and a fake scan:
Read the rest of this entry »
Posted in Troubleshooting | Tagged: Malware, Process Monitor | 2 Comments »
Understanding and Troubleshooting the Windows Temp Profile
Posted by William Diaz on February 17, 2011
When there is a mismatch between the local profile of a domain user and the network profile, you are going to run into a scenario where the user is logged on with a temp profile. The problem becomes apparent when the user sees only a standard desktop, which is missing their previous saved customizations and personal settings. This profile is created from the Default user account in C:\Documents and Settings\Default User + the settings applied by group policy and logon scripts. When this occurs, it is important to know why so that we can identify the problem and correct it.
When you logon for the first time with a new profile, that profile is created in C:\Documents and Settings\username. As you begin working and personalizing the desktop, programs, Windows appearances, connecting to printers, etc, these settings become a permanent part of your profile. In an environment where roaming profiles are enabled these personalization’s are also written to some network location (e.g. the local office file server) so that they can follow you to other workstations you log on to. Your roaming profile is composed of various folders and files copied from your local profile, e.g. Favorites, Contacts, Application Data, and most importantly ntuser.dat, also known as HKCU, the part of the registry that contains all your configurations. The roaming profile is written to the network profile when you log off each time and any changes made locally are merged to the profile on the network share afterwards. The next time you logon to that workstation, the profile on the local computer and network are compared. If there is a mismatch, then you run into a Windows logon prompt similar to this.
Read the rest of this entry »
Posted in Troubleshooting | Tagged: Malware | 6 Comments »
Just When You Thought You Had A Virus
Posted by William Diaz on November 15, 2010
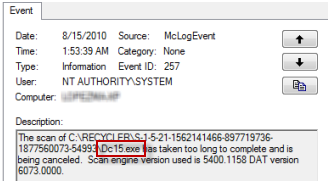
When troubleshooting an issue some time ago, I inadvertently came across a number of exe files residing on a user’s system. I stumbled across them while looking at the Windows Event Viewer and thought the name sounded suspicious:
Read the rest of this entry »
Posted in Inside Windows | Tagged: Malware | Leave a Comment »
Manual Discovery and Removal of Malware
Posted by William Diaz on October 6, 2010
If you have not had a chance, set aside some time to watch Advanced Malware Cleaning, an excellent webcast by Mark Russinovich. I used some of the techniques from that presentation to identify and remove malware on systems I have come across.
In the case here, the user would open Internet Explorer but was not able to connect to the Internet. This would happen a couple times a day. The problem was tracked down to the Proxy field not populating with the office ISA address and the field remained grayed out so it could not be toggled on directly. The issue could be worked around temporarily by editing the registry to enable the proxy but at some point it was getting removed again. I was already suspicious that this was related to malware because each day the user logged on, the virus protectionsuite would catch the same Dlls’ attempting to downloaded to the system and being deleted.
I would be using Process Explorer and Autoruns as my tools. Here were the first things I noticed:
Read the rest of this entry »
Posted in Troubleshooting | Tagged: Autoruns, IE, Malware, Process Explorer | Leave a Comment »
The Case of the Persistent IE Security Prompts
Posted by William Diaz on October 2, 2010
In an earlier post, I blogged about a request where the user no longer wanted to be annoyed by the IE’s security information prompt when visiting secure sites and the problem involved in trying to circumvent this setting in an environment where this is controlled via group policy. This time, I came across an issue where the user was being interrupted by the same prompt when visiting an internal resource that should not be displaying the IE “Security Information” prompt for secure sites.

Read the rest of this entry »
Posted in Troubleshooting | Tagged: Autoruns, Internet Explorer, Malware | Leave a Comment »
Advanced Malware Cleaning
Posted by William Diaz on July 18, 2010
Posted in Troubleshooting, Troubleshooting Tools | Tagged: Malware | Leave a Comment »
The Case of the Hidden Scheduled Tasks
Posted by William Diaz on July 9, 2010
This case provided a good opportunity to use Sysinternal’s Autoruns to detect and remove some malware that had found its way onto one of our workstations. What was happening was that some unknown process on this workstation was going out to the Internet at the same time every hour and attempting to download a suspicious executable named Zl0.exe and drop in it the local temp folder for the user, which by default is C:\Documents and Settings\username\Local Settings\TEMP\ for Windows XP (actually, we redirect this to a custom folder).
We knew this because our virus protection had been configured to stop all unknown exe files from writing to or starting from from this location. The attempt to download the file was stopped by the host intrusion detection but the process responsible for trying to download it was undetected.
Before starting, I verified Zl0.exe was, in fact, malware by searching it on the Internet. A quick scan of the system’s running processes with Process Explorer didn’t reveal anything out of the ordinary. Since the download was taking place each hour, I assumed the Windows Task Scheduler job was involved. The Task Scheduler is actually a service hosted within svchost.exe, along with many other services, so killing the process was not really practical. Another advantage to relying on the Task Scheduler was that the suspicious process could be started by a legitimate process, run, attempt to do what it wants to do, stop, and when you go to investigate with process monitoring utilities, it is not detected.
To confirm my suspicion, I opened the Task Scheduler. However, there were no abnormal scheduled jobs, even after checking the View Hidden Tasks from the Advanced menu:
Posted in Troubleshooting Tools | Tagged: Autoruns, Malware | Leave a Comment »
