Just When You Thought You Had A Virus
Posted by William Diaz on November 15, 2010
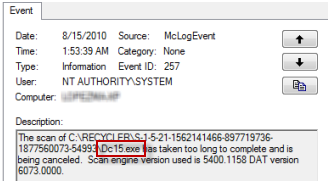
When troubleshooting an issue some time ago, I inadvertently came across a number of exe files residing on a user’s system. I stumbled across them while looking at the Windows Event Viewer and thought the name sounded suspicious:
I opened the recycle bin but it was empty. I already had Process Monitor running so I decided to set a filter on the process querying the file and saw this:

Worse yet, I looked inside one of the operations and saw references to several other files with different file formats but similar names

Unsure what it was, I searched the Internet for Dc15.exe (along with .lnk .vbs .xls .url) and scrolled through page after page of “victims” reporting that they had become infected and how no virus scanner yet was able to detect these files as threats and delete them. There are even threat analytics on the “Dc##.exe” virus, numerous reports of odd behavior since it was discovered on the infected system, burning buildings and mass hysteria. You can even see our virus scanner is the process scanning the file and not detecting it as malicious!
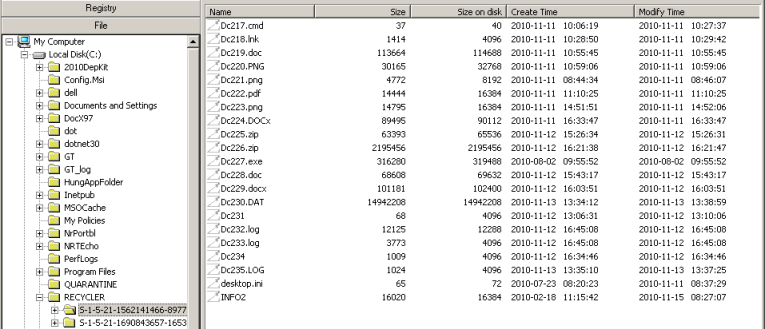
Convinced, I went into the command shell since it revealed the “super” hidden files, navigated to the recycle bin/SID of the user and deleted everything. The next day I continued troubleshooting the same workstation again and, amazingly, came across another one, Dc29.exe:

I even went so far as to install a rootkit detector to remove the file streams.

The thing you should know about rootkit detection software is that it looks at everything hidden from Windows but does not explain to you that hidden objects are not strictly malicious software. It wasn’t until I came across these on my own workstation (which is clean as a whistle, of course) that I knew these could not be malicious. Poking around with a utility that looks at file and reg keys hidden from the Windows API I saw this:
You really have to look harder at your search results to see this little Microsoft KB article: http://support.microsoft.com/kb/136517. Here’s what it was to say:
Each hard disk contains a hidden folder named Recycled. This folder contains files deleted in Windows Explorer or My Computer, or in Windows- based programs.
When you delete a file, the complete path and file name is stored in a hidden file called Info or Info2 (Windows 98) in the Recycled folder. The deleted file is renamed, using the following syntax:
D<original drive letter of file><#>.<original extension>
Examples:
New file name:
Dc1.txt = (C drive, second file deleted, a .txt file)
INFO file path:
C:\Windows\Desktop\Books.txt
New file name:
De7.doc = (E drive, eighth file deleted, a .doc file)
INFO file path:
E:\Winword\Letter to Rosemary.doc

Leave a comment