AIM Network Logging Reveals Windows Passwords
Posted by William Diaz on January 27, 2011
I was asked to troubleshoot a user’s connectivity issues with AIM. I am not too enthusiastic about anything AOL related but I would look anyway. One of the things I wanted to do was see if AIM had some internal network logging built into it. Starting with version 7.5.8.2 there is an option that resides under Settings > Connection that enables diagnostic network logging.
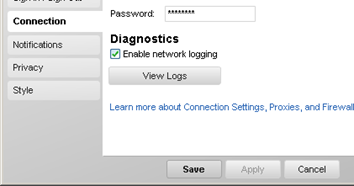
I enabled this setting and the next day examined the user’s logs, which are written to Documents and Settings\username\Local Settings\Application Data\AIM\Logs. I was surprised to see the user’s Windows logon information being written to the log in clear text. How does it obtain this information? We are behind a proxy so the user’s Windows logon credentials need to be populated in the proxy connection settings in AIM and are outputted to the network log:

AIM makes no attempt to mask this information (and, yes, the username and password have been modified intentionally).
Now, even though this is not turned on by default can be turned on by anyone with admin access to system by navigating to C:\Documents and Settings\username\Local Settings\Application Data\AIM\Settings and opening global.xml and adding the highlighted line below:
The next time the user logs onto the system in a Proxy environment and opens AIM, the network log file will be created and the Windows username/password—not the AIM username/password—will be written in plain text.

Leave a comment